Security basic best practice for Users
Denis A Nicole
2004-08-27
[this was prepared as a result of discussion at the Faculty IT Forum meeting
on 2nd September 2003]
*** Don't forget to install Windows XP
Service Pack 2 ***
Background
Backups
You will suffer inconvenience and lose data as a result of hostile
hacking, by virus attack or otherwise, on your system. We need to keep the
threat in proportion; it is perhaps comparable to the very real and actual risks
of having your laptop stolen, having the building burn down, or having your
workstation stolen or damaged during a break-in. All these things happen
regularly and your only real protection is regular backups to non-volatile
media. Your School may do this for you, or you may choose regularly to write CDs
yourself, but it must be done. Data stored in only one place does not really
exist. You will receive little or no sympathy over data lost from a workstation
or laptop.
So, above all else for your own protection, you need to ensure that you have
a systematic and regular backup process. You should also ensure that your
backups can be read on systems other than the one which created them. It is easy
to fall into a false sense of security while writing unreadable tapes/CDs.
[somebody should expand on how to do this...]
Security
Backups provide your ultimate protection. Security allows you to get on with
your work. There are other important reasons to keep your system secure:
- You might want to keep your own data private; you are obliged to protect
data about other individuals and other confidential material.
- An insecure machine is a threat to other systems at our site. There have
been serious incidents in which old under-maintained machines running old
and unpatched versions of an operating system have fallen under the control of an
outside hacker and been used to harvest passwords. Recent serious infections
have resulted from contaminated laptops being brought into the University and
plugged into the network behind a firewall.
- You are not paid to spend you time (or somebody else's) disinfecting and
rebuilding systems because of your carelessness.
- If you machine is taken over and run as a pornography server (it has
happened), how will you explain to the police?
The effective use of IT resources is an essential part of the business
activities of the University. Deliberate interference with this part of
University life is not treated lightly; abusers have been prosecuted.
Support
These notes will not make you an expert on system security. I'm not one.
While the principles remain the same, the details of attacks and vulnerabilities
change quite rapidly and you really need to be a full-time professional support
person to be able to keep up with what is happening. We have some very good
support staff in the University. Indeed, one of the
principal anti-virus and
anti-spam tools is written and maintained by one of our people. The
University is only rarely deliberately targeted but, when it has happened, they
have responded professionally and effectively by protecting our users and
catching the culprits. Most of the time, however, the problems are part of a
wider attack on the Internet community.
It is for you and your support team to agree the degree of involvement you
and they have in the management of your computer systems. You are probably best
off letting them do as much as they are willing; the notes below are to help you
understand what is happening, an to protect systems that they cannot manage for
you.
Passwords and Remote Access
[Don't use easy to guess passwords. Never use telnet or password-protected
ftp. Ssh2 and scp are the modern alternatives.]
Email
[Attachments and mail browser bugs are the main entry points for current
viruses. Make sure your School runs
Mailscanner. Don't run smtp yourself.
Never ever rise to the bait and reply to spam; it only confirms your valid
address. Don't open web pages that arrive in spam either; that too is a way of
confirming addresses. Sometimes web links can be barely visible...]
Windows Systems
First, if at all possible, you should be running the most recent stable
version of the operating system. This is currently Windows XP. Old OSes are not
maintained as rigorously and lack modern security features. Beyond that, there
are several important protections, which follow closely Microsoft's advice
Protect your PC:
Security Centre
This is a new feature of Windows XP service pack 2. Amongst other things, it
manages automatic updates to the Operating System; you shouldn't need to use
Windows Update manually at all.
Windows Update
Windows Update requires you to use the Internet Explorer browser that comes
with Windows; Update is normally installed on your Start menu but you
can also access it directly at
http://windowsupdate.microsoft.com. You can also enable
automatic updates using
Start->(R-click) My Computer->Properties->Automatic Updates
You should check daily for critical updates. You
should also check for Microsoft Office updates at
http://office.microsoft.com/productupdates/. This is probably the most
important protection for your system.
It is, however, not all completely straightforward. A gotcha with the Windows Update system on Windows XP; patch 811494 (M502-013) was superseded without changing the patch number. So, Windows Update will not update the patch and you have to install it manually. The symptom of the problem is poor disk performance.
Sophos (applies in this form to U Southampton users only)
The notes below are out of date. They still work, but the modern way to
automate update of both Sophos itself and the virus signatures is by using the
Sophos Remote Update software
and either the School or University server.
You need to install Sophos itself, from
http://www.software.soton.ac.uk/software/Sophos/ ; you want the latest
Product: Sophos Anti Virus Toolkit vX.XX
OS: WinNT/2000/XP
This is a password protected page for which you need your ISS (SUCS) user ID and
password.
Just follow the instructions for the default configuration.
If your computer is in a Domain, it is possible to have both the Sophos
program itself and the set of virus signatures automatically updated by a
special program. This requires a special installation of Sophos. You will not be able to set this up yourself; your Domain
Administrator has to enter the password for the sweepupd
user during the installation. There are lots of implications if you decide to
join a Domain; I normally choose not to.
Outside a domain, you can only autoupdate the virus signatures. To do this
you need the sget web downloader which is provided by Sophos; it is at
http://www.software.soton.ac.uk/software/Sophos/sget.exe and it needs to go
in your "%ProgramFiles%\Sophos SWEEP for NT" directory.
This is a password protected page for which you need your ISS (SUCS) user ID and
password.
Copy this update.cmd script to the
same place. It needs to be run at least daily:
set VERSION=382
%SystemDrive%
cd %ProgramFiles%
cd "Sophos SWEEP for NT"
sget http://www.sophos.co.uk/downloads/ide/%VERSION%_ides.exe
del *.ide
%VERSION%_ides.exe
del %VERSION%_ides.exe
net stop sweepsrv.sys
net start sweepsrv.sys
date/t
time/t
Set VERSION appropriately for the Sophos version X.XX you have
installed. Note that, unless you unpack the .ide files in a separate
directory, you really do need to delete the old ones before unpacking 373_ides.exe,
or the unpack might fail. You can run this manually or, alternatively,
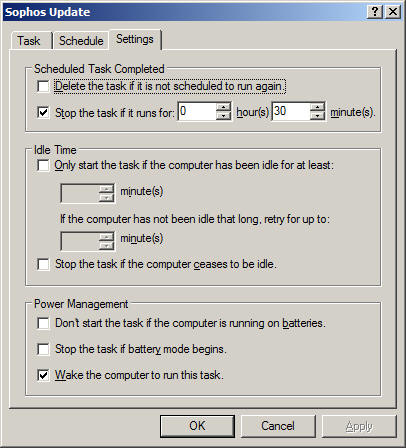
you can automate it to run daily at, say, 04:30. Go to
Start->Control Panel->Scheduled Tasks->Add Scheduled Task
and follow the instructions. My scheduled task looks like this:


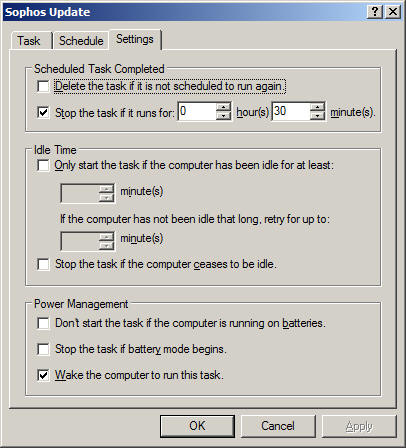
and yes, I did have to enter my password.
You also need to update the Sophos program itself monthly by hand,
by reinstalling it from the University web site and you need to update VERSION
in the above script appropriately.
For further information, see
http://www.sophos.com/support/faqs/comdown.html.
Free Anti-Virus Software
If you do not have the right to use Sophos, there are alternatives:
Anti-Spybot Software
Microsoft Internet Connection Firewall for XP
You want to run this on all your machines. It is vital for systems
outside University and School firewalls, it is also a good idea if you are
inside. Follow the instructions at
http://www.microsoft.com/WINDOWSXP/home/using/howto/homenet/icf.asp. I only
enable a few ports on my workstation:
- Remote Desktop: so I can log in from home.
- SMB: so I can enable file and printer sharing. I added this port manually,
the properties are:
Description of Service: SMB
Name of computer: <my workstation
name>
External Port: 139
Internal Port: 139
TCP
- NetMeeting: The Microsoft ICF is a bit special in that it allows
applications such as NetMeeting to create holes on demand. Nevertheless, if
you want to accept a direct connection (without using a server) from another
NetMeeting user, you need to make two openings in the firewall:
Description of Service: H.323
(NetMeeting incoming)
Name of computer: <my workstation
name>
External Port: 1720
Internal Port: 1720
TCP
Description of Service: Audio Call
Control (NetMeeting)
Name of computer: <my workstation
name>
External Port: 1731
Internal Port: 1731
TCP
Interestingly, the Audio Call Control port does my seem to be needed
for audio or video; it is necessary for setting up Whiteboard etc. See also:
http://support.microsoft.com/default.aspx?scid=http://support.microsoft.com:80/support/kb/articles/Q158/6/23.asp&NoWebContent=1.
Depending on your machine configuration, you may wish to add a few other
ports such as RPC/DCOM (For Microsoft Exchange) at 135. Leaving that one out
would, however, have saved you from the recent MSBlaster worm. You definitely do
not want to enable the well-known-risk services FTP, Telnet or TFTP.
Microsoft Baseline Security Analyser
This is mainly a check on the way you have configured your system, with open
accounts, weak passwords etc.; it can be found at
http://www.microsoft.com/technet/treeview/default.asp?url=/technet/security/tools/Tools/mbsahome.asp.
Download it; run it; do what it says.
Malware
Even with the standard precautions, I still get infected with malware. There
are several useful places to look in order to get rid of unwanted periodic
pop-ups etc. On my list for Windows are:
- Internet Explorer downloaded objects: Look in Tools->Internet
Options->General->Settings...->View Objects... Delete anything you don't
recognise as safe; if you really needed it, you will be prompted to reload it
over the web when necessary.
- Make sure you recognise all the periodic tasks in Start->Control
Panel->Scheduled Tasks.
- Check for unexpected services in Start->Control Panel->Administrative
Tools->Services.
- Check for unexpected scripts in Start->All Programs->Startup.
- Search the registry for suspect URLs by running Start->Run...->regedit
and Edit->Find... Be careful though, deleting the key might have
unfortunate side effects. A few interesting places are:
- HKEY_CURRENT_USER\Software\Microsoft\Internet
Explorer\SearchUrl
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Runonce
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Run
- HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\Runonce
Other useful odds and ends
These are not so much for use as to warn you what's out there.
- Active Ports from
http://www.ntutility.com/freeware.html monitors local network ports on you
machine and lets you see what's happening. Of course, a hostile virus may only
communicate briefly; it may be hard to spot. Don't trust the Windows Task
Manager to tell you what's going on either; its fairly easy to hide from.
- SuperScan from
http://www.foundstone.com/resources/scanning.htm looks for open
ports on other machines; please only point it at your own kit. Of course, even
if there are no unexpected ports open, there is the real danger that a virus
might have subverted a standard port; I once found an ftpd sitting on
the Remote Desktop port.
- L0phtCrack from
http://www.atstake.com/research/lc/ is a well-known shareware Windows
password cracker. John the Ripper from
http://www.openwall.com/john/ is free. These are useful for understanding
what constitutes a weak
password. Again, run them only on your own kit.
- A boot disk for editing the Windows Registry and changing passwords etc.
is at
http://home.eunet.no/~pnordahl/ntpasswd/. It's not hard to crack BIOS
passwords (though the method varies from machine to machine) so this disk is a
clear warning not to allow the bad guys physical access to your system.
Of course, the same trick is even easier on Linux systems, where the file
system and /etc/passwd formats are properly documented.
Linux Systems
[Run the latest RedHat. Keep it regularly updated. Enable the firewall. Run
Sophos?]